How to Block Emails from Onmicrosoft.com Domains
Block spam emails from onmicrosoft.com domains using Exchange Online mail flow rules while allowing legitimate organizational communications. Create transport rules with sender domain conditions and exceptions to filter unwanted messages from default Microsoft 365 tenant domains.
A notable challenge for Microsoft 365 admins worldwide is handling the surge of spam emails that appear as if they originated from legitimate onmicrosoft.com addresses📩. This tactic bypasses basic filters, making it critical for admins to have a multi-layered defense strategy🔒.
As an administrator, you have several options to block unwanted incoming emails such as message delivery restrictions, tenant allow/block list, anti-spam policies, and so on. To specifically block spam emails from the onmicrosoft.com domain, you can use Exchange Online transport rules.
In this guide, we will help you address this common challenge faced by many Microsoft 365 admins.
When setting up a Microsoft 365 tenant, every organization is assigned a default domain that ends with “onmicrosoft.com.” This domain is used primarily for administrative purposes and is automatically assigned to all new Microsoft 365 accounts. For example, if your organization is named “ExampleCorp,” the default domain would be “examplecorp.onmicrosoft.com.”
While this domain serves specific functions, it can sometimes be a source of unwanted or spam emails. Blocking spam emails can help reduce clutter and enhance security. However, you might still need to allow legitimate emails from your own organization’s “onmicrosoft.com” domain. Here’s how you can manage this.
Blocking emails from the “onmicrosoft.com” domain can be achieved using mail flow rule in Exchange Admin Center (EAC).
To block incoming emails from the onmicrosoft.com domain, you can create a transport rule in Exchange Online by following the steps below.
Step 1: Go to the Exchange Admin Center
.
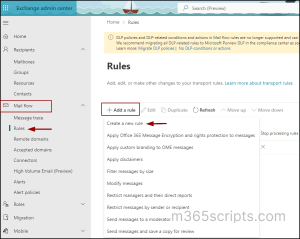
Step 2: Navigate to the ‘Mail flow’ dropdown -> Select ‘Rules’.
Step 3: Click on ‘+ Add a rule’ and select ‘Create a new rule’.
Set Rule Conditions
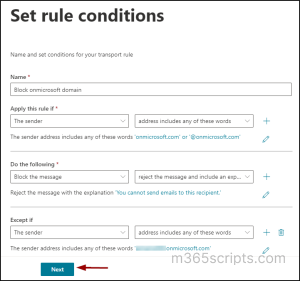
Step 4: Name your mail flow rule. For example, something like
“Block onmicrosoft domain.”
Step 5: In the ‘Apply this rule if’ section, select ‘The sender’ in the first dropdown, and ‘address includes any of these words’ in the second dropdown.
Step 6: In the ‘Specify words or phrase’ field, enter ‘onmicrosoft.com, @onmicrosoft.com’ -> Click ‘Add’ and then ‘Save’.
- @onmicrosoft.com: This pattern will match any email address that ends with @onmicrosoft.com, ensuring all emails from this domain are caught.
- onmicrosoft.com: This pattern will match any email address that contains onmicrosoft.com, providing a broader catch for any possible variations.
Step 7: In the ‘Do the following’ section, select ‘
Block the message’, and then select ‘Reject the message and include an explanation’ in the values dropdown.’ Depending on your requirements, you can also move these emails to quarantine by adjusting the conditions.
Step 8: Provide an explanation text, such as “You can’t send emails to this recipient” in the ‘Specify rejection reason’ field -> ‘Save’.
This condition sends a non-delivery report (NDR), also known as a bounce message, back to the sender with the specified rejection text. The recipient will not receive the original message or any notification. To prevent emails from your organization’s “onmicrosoft.com” domain from being blocked, you can add an exception to the rule.
Step 9: In the ‘Except if’ section, select ’The sender’, and then choose ‘address includes any of these words’ in the values dropdown. Then in the ‘Specify words or phrases’ field, enter <yourorg.onmicrosoft.com> -> ‘Add’ –> ‘Save’.
Step 10: Click ‘Next’.
Set Rule Settings
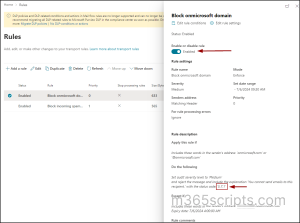
- Keep the mode value as the default ‘Enforce’ to activate the rule immediately.
- Specify severity according to your preference
- Select the ‘Activate this rule on’ checkbox and set the rule activation date.
- Set the rule deactivation date if any.
- Leave other options as it is.
- Add descriptive comments about the rule in the comment box.
- Click Next.

Review and Finish
In the ‘Review and Finish’ section, carefully review all the conditions set for the transport rule before proceeding to click the Finish button.

Once the rule is created successfully, click Done.
⚠️ Important: Note that the rule will initially be created in a disabled state. You must enable it for it to take effect and start working. Select the created rule in the ‘Rules’ page and enable the toggle as shown below.
Here, you can see that the default enhanced status code used is 5.7.1. It indicates that an email message was rejected. This happens when the sender isn’t authorized to email the recipient, often due to policy settings, such as your transport rule.
Tip: Like the above, you can configure mail flow rule to filter spam mails and receive emails on unlicensed admin account. This helps protect and control overall email traffic in your organization.
If you are a PowerShell enthusiast, you can use this method to achieve the same result. For that, first, connect to EXO using PowerShell. Then, use the New-TransportRule cmdlet to create a transport rule to block emails from the onmicrosoft.com domain as below:
|
1 |
New-TransportRule -Name "Block onmicrosoft domain" -FromAddressContainsWords "onmicrosoft.com", "@onmicrosoft.com" -RejectMessageEnhancedStatusCode "5.7.1" -RejectMessageReasonText "You can’t send emails to this recipient" -ExceptIfFromAddressContainsWords "yourorg.onmicrosoft.com" |
This cmdlet creates a rule named “Block onmicrosoft domain” that rejects messages from sender address that contains “onmicrosoft.com” or @onmicrosoft.com, while exempting your organization’s domain. The cmdlet also enables the rule upon execution.
Similarly, you can use Anti-spam policies to remove all allowed domains within the organization, enhancing your email filtering settings.
Now that we’ve enabled the transport rule to block incoming emails from the onmicrosoft.com domain, let’s explore the sender’s experience. Imagine an organization named Fabrikam has configured this mail flow rule. Now, when a sender from contoso.onmicrosoft.com attempts to send an email to fabrikam.onmicrosoft.com, they will receive the following error & their email will not be delivered. As a result, Fabrikam will not receive the email in their inbox.
“Your message to user@fabrikam.onmicrosoft.com couldn’t be delivered. A custom mail flow rule created by an admin at org.onmicrosoft.com has blocked your message”.
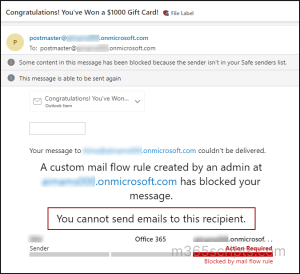
You can see the “You cannot send emails to this recipient” explanation phrase which we specified in the transport rule in the error message. The email address postmaster@<org>.onmicrosoft.com shown in the message typically indicates the administrative contact for your organization’s email domain. The postmaster address is a standard email address used for handling email-related issues, such as bounce-backs, delivery failures, and other administrative matters.
That’s it—you’re all set!
Closing Thoughts
In summary, by setting up a simple transport rule in the Exchange Admin Center, you can effectively block emails from default domain in Exchange Online while allowing legitimate emails from your own organization. This approach helps maintain a cleaner, more secure inbox for your users. Complement these efforts with additional email security measures such as external email tagging, email encryption, first contact safety tips etc. Furthermore, adhering to Microsoft 365’s best security practices is essential to protect your organization against potential intrusions.
We hope that this blog will give you detailed information on how to protect your organization from incoming email spam. Thanks for reading. For further questions, feel free to reach out to us in the comments section.