Opt-in to the Exchange Online Endpoint for Legacy TLS Clients using SMTP Auth
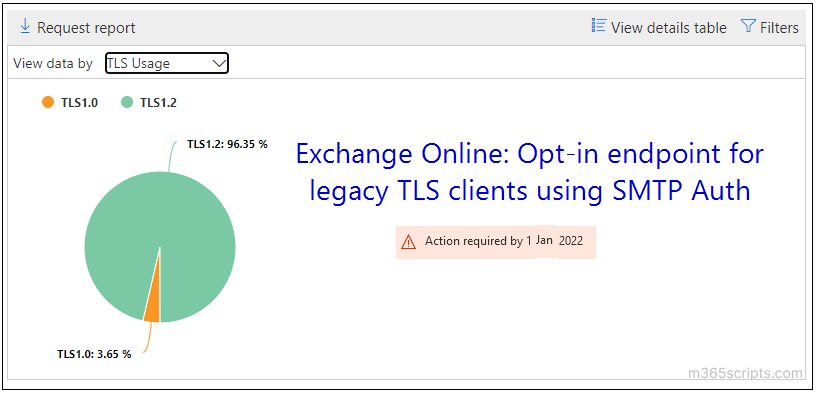
Configure legacy TLS endpoint opt-in for Exchange Online SMTP Auth clients using older TLS versions. Set AllowLegacyTLSClients property and use smtp-legacy.office365.com endpoint before Microsoft disables TLS 1.0 and 1.1. Review TLS usage reports to plan migration to TLS 1.2.
We all know that Exchange online ended support for TLS 1.0 and TLS 1.1 in 2020 to meet the security and compliance requirements. However, Microsoft still allows clients to use legacy TLS versions to connect with Exchange Online.
In 2022, Microsoft has planned to completely disable older TLS versions in Exchange Online to improve security. If your organization still uses clients that aren’t compatible with TLS 1.2, then the new opt-in endpoint can be set to use the previous versions of TLS.
To use legacy TLS versions, admins need to change the following settings.
- Use PowerShell to set AllowLegacyTLSClients to $true. Connect to Exchange Online PowerShell before running the following cmdlets.
To view the current status of the AllowLegacyTLSClients property, run the following cmdlet.
|
1 |
Get-TransportConfig | Format-List AllowLegacyTLSClients |
To opt-in, execute the below cmdlet.
|
1 |
Set-TransportConfig -AllowLegacyTLSClients $true |
- Configure clients and devices to use the new endpoint smtp-legacy.office365.com
admins can opt-out or force TLS 1.2 by checking the TLS usage report for SMTP in Exchange Online.
To disable legacy TLS, admins need to modify the following configurations.
- To set –AllowLegacyTLSClients to false, execute the cmdlet as follows.
|
1 |
Set-TransportConfig -AllowLegacyTLSClients $false |
- Configure clients to accept smtp.office365.com endpoint.
If you have not configured to use the legacy endpoint, you will get the following error message.
|
1 |
421 4.7.66 TLS 1.0 and 1.1 are not supported. Please upgrade/update your client to support TLS 1.2. Visit https://aka.ms/smtp_auth_tls |
The error occurs due to Exchange Online rejecting a small number of TLS 1.0 or 1.1 submissions.
I hope this blog will help you review and opt-in legacy client endpoint settings. You can share your experience using TLS 1.0/1.1 in the comment section.